Why App Security Is Critical for Startups in 2026
Every year, 60% of small businesses close within six months of experiencing a major data breach. For startups building mobile or web applications, this statistic represents an existential threat that most founders dramatically underestimate. Security vulnerabilities aren't just technical nuisances. They're business killers that can drain resources, destroy user trust, and end promising ventures before they scale. This guide explains why integrating security from day one isn't optional anymore, reveals the hidden costs of common vulnerabilities, and provides practical methods to protect your startup's app without breaking your budget or slowing development velocity.

Key takeaways
Point | Details |
|---|---|
Breach costs are catastrophic | Average data breaches cost $4.44 million, with mobile breaches reaching $6.99 million, often fatal for startups. |
Early security integration saves money | Shift-left DevSecOps and automated testing reduce vulnerability remediation costs by up to 80% compared to post-launch fixes. |
Automated tools miss critical flaws | Manual penetration testing catches complex business logic vulnerabilities that scanners overlook, preventing chained exploits. |
Security investment delivers massive ROI | Professional penetration testing provides returns exceeding 51,000% when compared to average breach costs. |
Mobile apps face escalating threats | 85% of organizations report increasing mobile attack frequency and sophistication in 2026. |
The rising risk landscape in app development for startups
The security threat environment for mobile and web applications has intensified dramatically. Global average data breach costs reached $4.44 million in 2025, with mobile-specific breaches climbing to $6.99 million per incident. For bootstrapped startups operating on tight budgets, a single breach of this magnitude represents complete financial annihilation. These aren't abstract corporate problems. They're immediate existential risks that determine whether your company survives its first year.
Mobile applications have become prime targets for sophisticated attackers. 85% of organizations report rising mobile attacks in frequency and complexity throughout 2025 and into 2026. Attackers exploit the distributed nature of mobile apps, targeting everything from insecure data storage to vulnerable API endpoints. The attack surface expands with every device your app touches, every third-party SDK you integrate, and every backend service you connect.
Despite growing awareness, many startups maintain dangerous overconfidence in their security posture. Organizations consistently report security incidents even when leadership believes protective measures are adequate. This confidence gap creates blind spots where vulnerabilities flourish undetected until exploitation occurs. The disconnect between perceived and actual security creates a dangerous illusion that leaves startups exposed.
Professional penetration testing delivers extraordinary return on investment when measured against breach costs. With average breach remediation exceeding $4 million and comprehensive penetration tests costing $5,000 to $15,000, the ROI calculation is straightforward. A single prevented breach generates returns of 26,000% to 88,000% on the testing investment. For startups, this math transforms security from a cost center into a survival mechanism.
Understanding mobile app types and threats specific to your platform helps prioritize security investments effectively. Different app architectures present unique vulnerability profiles that require tailored defensive strategies.
Core security methodologies every startup should implement
Secure Software Development Life Cycle (SDLC) with shift-left DevSecOps forms the foundation of modern app security. Shift-left DevSecOps integrates security testing from the earliest development stages rather than treating it as a pre-launch checklist item. This approach catches vulnerabilities when they're cheapest to fix, during initial coding rather than after deployment. Security becomes embedded in your development culture instead of being an external audit that delays releases.
The OWASP Mobile Top 10 provides a battle-tested framework for addressing the most critical vulnerabilities in mobile applications. Key protections include rigorous input validation to prevent injection attacks, comprehensive supply chain security for third-party dependencies, and secure data storage mechanisms that protect sensitive information even if a device is compromised. These aren't theoretical concerns. They're the exact attack vectors that have destroyed countless startups.
Pro Tip: Implement input validation on both client and server sides. Client-side validation improves user experience, but server-side validation actually protects your data since attackers can bypass any client-side controls.
Encryption at rest and in transit protects data throughout its lifecycle. At rest encryption secures stored data using strong algorithms like AES-256, ensuring that even physical device compromise doesn't expose sensitive information. In transit encryption via TLS 1.3 protects data moving between your app and backend services, preventing man-in-the-middle attacks. Both layers work together to create defense in depth.
Strong authentication mechanisms dramatically reduce unauthorized access risks:
Multi-factor authentication (MFA) requiring something users know (password) plus something they have (device token) or are (biometric)
Biometric authentication leveraging device capabilities like fingerprint or face recognition
Secure session management with appropriate timeout periods and token rotation
Account lockout policies after repeated failed authentication attempts
Least privilege principles minimize damage from compromised accounts or insider threats. Every user, service, and process should have only the minimum permissions required to perform its legitimate functions. This containment strategy limits breach scope when (not if) a security incident occurs. Your database service doesn't need file system access, and your analytics service doesn't need user credential databases.
Continuous security testing combines automated and manual approaches for comprehensive coverage. Static Application Security Testing (SAST) analyzes source code for vulnerabilities during development. Dynamic Application Security Testing (DAST) examines running applications for exploitable weaknesses. Regular penetration testing by security experts identifies complex vulnerabilities that automated tools miss. This layered testing strategy catches different vulnerability types at different development stages.
Security Control | Implementation Effort | Ongoing Cost | Risk Reduction |
|---|---|---|---|
Encryption (at rest/transit) | Medium | Low | High |
Multi-factor authentication | Medium | Low | Very High |
Input validation | High | Low | High |
Automated SAST/DAST | Low | Medium | Medium |
Manual penetration testing | Low | Medium | Very High |
Least privilege access | Medium | Low | High |
Integrating security throughout your end-to-end app development process ensures protection becomes automatic rather than an afterthought.
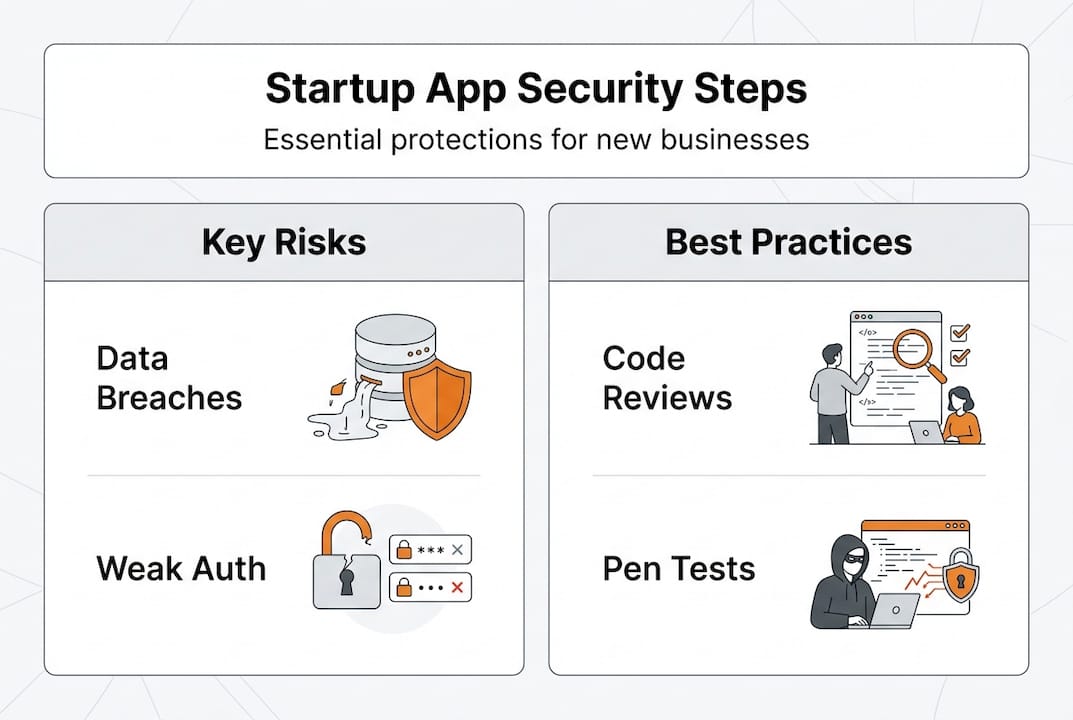
Understanding complex security pitfalls: beyond common vulnerabilities
Business logic flaws represent some of the most dangerous yet overlooked vulnerabilities in modern applications. Unlike technical vulnerabilities that security scanners detect, business logic flaws exploit gaps in how your application enforces rules and workflows. A chained business logic flaw enabled a $999,999 theft by exploiting five separate logical weaknesses that individually seemed harmless but together created catastrophic exposure. These vulnerabilities arise from assumptions developers make about how users will interact with features.
Missing authorization checks create pathways for attackers to access data and functionality they shouldn't touch. A single missing authorization check caused a full production data breach by allowing any authenticated user to access any other user's sensitive information simply by changing an ID parameter. The vulnerability existed because developers assumed the application UI would prevent users from requesting unauthorized data, forgetting that attackers bypass UIs entirely. This type of flaw is invisible to automated scanners that can't understand your application's intended access control model.
Small configuration mistakes cascade into major security incidents. A misconfigured cloud storage bucket, an overly permissive API endpoint, or a forgotten debug mode in production can expose your entire database. These issues often survive code reviews because they exist in configuration files, deployment scripts, or infrastructure definitions rather than application code. They're the security equivalent of leaving your back door unlocked while installing an expensive alarm system on the front entrance.
Pro Tip: Create a pre-deployment security checklist that specifically covers configuration items like debug modes, API authentication, cloud storage permissions, and logging settings. Configuration vulnerabilities are easy to prevent but devastating when missed.
Chained vulnerabilities multiply attack impact by combining multiple weaknesses:
Information disclosure reveals internal system details
Exposed details enable authentication bypass
Bypassed authentication grants access to privileged functions
Privileged functions contain injection vulnerabilities
Injection vulnerabilities provide complete system compromise
Each individual weakness might seem low severity in isolation, but attackers chain them into critical exploits. Automated tools analyze vulnerabilities independently and miss these dangerous combinations.
Detection Method | Business Logic Flaws | Missing Authorization | Configuration Errors | Chained Vulnerabilities |
|---|---|---|---|---|
Automated SAST | Poor | Poor | Good | Poor |
Automated DAST | Poor | Fair | Good | Poor |
Manual Penetration Testing | Excellent | Excellent | Excellent | Excellent |
Code Review | Good | Good | Fair | Fair |
Manual penetration testing by experienced security professionals remains essential despite advances in automated tooling. Human testers understand business context, recognize logical inconsistencies, and think creatively about attack chains that tools cannot conceive. They test your application the way real attackers will, combining technical exploitation with business logic manipulation. For complex applications handling sensitive data or financial transactions, manual testing isn't optional.
Addressing industry-specific app security requirements ensures compliance and customer trust in regulated sectors.
Practical steps for startups to embed security in app development
Adopting shift-left DevSecOps early transforms security from a bottleneck into a competitive advantage. Startups should integrate security testing into CI/CD pipelines from their first sprint, making security validation automatic with every code commit. This approach catches vulnerabilities immediately when context is fresh and fixes are simple. Waiting until pre-launch security audits discovers problems when remediation is expensive and delays are costly.
OWASP checklists provide actionable security requirements without requiring deep security expertise. The OWASP Mobile Application Security Verification Standard (MASVS) breaks down security into testable requirements across architecture, data storage, cryptography, authentication, network communication, and platform interaction. Each requirement includes clear pass/fail criteria that developers can verify. These checklists translate abstract security principles into concrete implementation tasks.
Automating security scans in your CI/CD pipeline creates continuous security validation:
Integrate SAST tools to analyze every code commit for vulnerabilities
Configure DAST scanners to test staging deployments before production
Implement dependency scanning to detect vulnerable third-party libraries
Set up security gates that block deployments containing critical vulnerabilities
Generate automated security reports for every release
Third-party library vetting protects against supply chain attacks that have compromised numerous high-profile applications. Every SDK, framework, and package you integrate expands your attack surface with code you didn't write and can't fully audit. Vet libraries by checking security advisories, reviewing maintenance activity, assessing community trust, and monitoring for known vulnerabilities. Popular doesn't mean secure, and convenience doesn't justify risk.
Pro Tip: Maintain a software bill of materials (SBOM) documenting every third-party component in your application. When vulnerabilities are disclosed, you'll know immediately whether you're affected and which apps need updates.
Scheduling quarterly manual penetration tests catches complex vulnerabilities that automated tools miss. Professional penetration testers bring adversarial thinking and business context understanding that scanners lack. They identify business logic flaws, test authorization boundaries, chain multiple weaknesses, and provide remediation guidance. Quarterly cadence balances thoroughness with cost, ensuring new features receive security validation before accumulating technical security debt.
Balancing security investment requires understanding ROI and risk mitigation. Given that 60% of small businesses fail within six months of a breach, security investment isn't overhead, it's survival insurance. A $10,000 annual security budget (automated tools plus quarterly penetration tests) prevents potential $4 million breach costs and company extinction. The math isn't complicated. The challenge is making security tangible before experiencing a breach.
Implementing mobile app scalability alongside security ensures your protections scale with user growth. Modern AI-native app development introduces new security considerations around model security and data privacy.
Secure your startup's app development with expert partners
Building secure applications requires specialized expertise that many startups lack in-house during early stages. TouchZen Media specializes in developing secure mobile and web applications for startups, integrating security best practices from initial architecture through deployment and scaling. Their California-based app development team brings deep experience in iOS and Android security, implementing encryption, authentication, and secure coding standards as foundational elements rather than afterthoughts.
Partnering with experienced development teams accelerates secure app delivery without the overhead of building internal security expertise. TouchZen's top UX designers balance security requirements with user experience, ensuring protection doesn't compromise usability. Their app development experts provide ongoing security guidance, helping startups navigate evolving threats and compliance requirements as they scale. For founders focused on product-market fit and growth, partnering with security-conscious developers lets you build on a secure foundation from day one.
Frequently asked questions
Why is security especially important for startups in app development?
Startups face disproportionate risk from security breaches because they lack the financial reserves and reputation resilience of established companies. A breach that costs $4 million represents a recoverable setback for a large corporation but complete annihilation for a seed-stage startup. Additionally, early security compromises establish patterns of technical debt that become exponentially more expensive to remediate as the codebase grows and user base expands.
What are the most effective methods to integrate security into the development process?
Shift-left DevSecOps embedding security testing in CI/CD pipelines provides continuous validation with minimal friction. Automated SAST and DAST tools catch common vulnerabilities immediately, while quarterly manual penetration testing identifies complex business logic flaws and chained vulnerabilities that scanners miss. Combining automated and manual approaches creates comprehensive coverage across technical and logical vulnerability types.
How can startups balance security budgets with rapid development needs?
Prioritize automated security testing integrated into existing development workflows to maximize coverage while minimizing manual effort and delays. Use penetration testing ROI data (26,000% to 88,000% returns) to justify quarterly professional assessments to stakeholders and investors. Embedding security early costs 80% less than retrofitting security after launch, making it the most cost-effective approach even for resource-constrained startups.
What are examples of hidden vulnerabilities that automated tools miss?
Business logic flaws exploiting workflow assumptions, missing authorization checks allowing unauthorized data access, and chained vulnerabilities combining multiple low-severity issues into critical exploits consistently evade automated scanners. These vulnerabilities require human understanding of application context, business rules, and creative attack thinking that current automated tools cannot replicate. Manual penetration testing by experienced security professionals remains essential for detecting these sophisticated vulnerability types.